As an avowed 4G LTE Android enthusiast, I will confess to an obsession with anything that might pose a threat to my smartphone. It was thus with more than a bit of consternation that I read a series of articles in the past few days about a newly discovered Android security flaw that literally with a click can wipe out/wipe clean your device. Ouch!
The original item appeared on a site I visit often, Gizmodo, an admittedly Apple-biased place but one where there are always interesting tips on new things I can do with my device as Apple to the core fanatics can do with theirs.
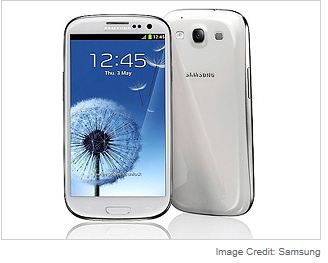
Author Jesus Diaz deserves credit for uncovering the flaw. It has been confirmed on the Samsung’s popular Galaxy II and AT&T’s Galaxy SIII phones along with any Samsung Android phones running the its TouchWiz user interface (UI). It also evidently has been known as an issue by Samsung for a while, and is not confined to their products alone.
Beware! How it works
The simple explanation that everyone needs to know is that by surfing via TouchWiz to any web page that contains the code “tel:*2767*3855%23" in an HTML frame,” you will have a lot more than your clock cleaned. It will be in fact your worst nightmare.
For those who want some technical details the way in which this nasty boy works is as follows: The HTML frame loads a tel: URL. This URL tells the device its content is a clickable telephone number. However, instead of a phone number, the URL contains a special USSD code that tells the phone to wipe out itself.
As Diaz notes, the term USSD means Unstructured Supplementary Service Data. This is a special number sequence that is used by wireless service providers to execute instructions in your phone. He also was kind enough to provide a list of phones that have been compromised:
Here's a list of the potentially compromised phones:
• Samsung Illusion SCH-I110 (TouchWiz 3.0)
• Samsung Infuse 4G (TouchWiz 3.0)[4]
• Samsung Rugby Smart (TouchWiz 3.0)
• Samsung Droid Charge
• Samsung Galaxy Gio (TouchWiz 3.0)
• Samsung Galaxy Fit (TouchWiz 3.0)
• Samsung Galaxy Mini (TouchWiz 3.0)
• Samsung Galaxy Mini 2 (TouchWiz 3.0)
• Samsung Galaxy 3 (TouchWiz 3.0)
• Samsung Galaxy 5 (TouchWiz 3.0)
• Samsung Captivate Glide (TouchWiz 4.0)
• Samsung Gravity Smart
• Samsung Exhibit II 4G (TouchWiz 4.0)
• Samsung Galaxy Y (TouchWiz 4.0)
• Samsung Galaxy W (TouchWiz 4.0)
• Samsung Galaxy R (TouchWiz 4.0)
• Samsung Galaxy Ace (TouchWiz 3.0)
• Samsung Galaxy Ace Plus (TouchWiz 4.0)
• Samsung Galaxy Ace 2 (TouchWiz 4.0)
• Samsung Galaxy Pro (TouchWiz UI v3.0)
• Samsung Galaxy Pocket
• Samsung Galaxy S (TouchWiz 3.0 / TouchWiz 4.0)
• Samsung Galaxy S Blaze 4G (TouchWiz 4.0)
• Samsung Galaxy S Duos (TouchWiz 4.0)
• Samsung Galaxy SL I9003 (TouchWiz 3.0 / TouchWiz 4.0)
• Samsung Galaxy S Plus (TouchWiz 3.0 / TouchWiz 4.0)
• Samsung Galaxy S Advance (TouchWiz 4.0)
• Samsung Galaxy S II (TouchWiz 4.0)
• Samsung Galaxy S II Skyrocket (TouchWiz 4.0)
• Samsung Galaxy S III (TouchWiz Nature UX)
Unfortunately (and this included me), reader Dylan Reeve says that the problem —executing a USSD code without user intervention from a website, or other delivery vector — in his experience also affects an HTC One X (running HTC Sense 4.0 on Android 4.0.3) and a Motorola Defy (running Cyanogen Mod 7 on Android 2.3.5). Mr. Reeve also was kind enough to suggest that if you are running the latest firmware for Galaxy S3 (4.0.4) you should not have a problem, and that the issue can be avoided by installing an alternative dialer app from Google Play.
Reeve is not the only one offering advice on what to do if you are nervous. Lots of people have weighed in. The consensus seems to be to do what may appear to be obvious but is good practice in any event.
1. Always avoid links that you are suspect of. I know from a bad click on Twitter just how bad things can get in a hurry.
2. Yes, by all means use an alternative dialer app for making calls that will not automatically execute the USSD instructions.
3. Make sure you have the latest firmware for your phone.
4. Make a daily backup of your phone to your computer so in the event of disaster you can be back in action quickly.
If you have questions as to whether you are running the latest firmware do the following: load your phone's Setting app and scroll down to About Device. Tap that, then the Software Update tab at the top of the next screen that appears. Then, tap Update on the following screen. Your phone will check for updates and install the latest if you're running an older version.
After reading the various items on this I followed the instructions above and to my relief I was on the latest firmware and until the next flaw is found have a lot more peace of mind. This really is a case where as the old bromide goes, “an ounce of prevention is worth a pound of cure.”