There has been an avalanche of research reports recently individually on the subjects of cloud adoption, usage and risks. However, there has yet to be one that combines information on all of them which is why the release today by Cupertino, Calif.-based Skyhigh Networks of its Cloud Adoption and Risk Report, is so fascinating. To my knowledge it is the first industry report to analyze not only the actual usage of cloud services but also the risks they present to organizations.
The big headline from the report can be summed up in its characterization that “Cloud is the New Wild Wild West.” Based on data gleaned from more than 100 organizations and their three million users, unfortunately that is a reasonable conclusion. What the report reveals is that most organizations lack the information to understand and mitigate a broader set of risks posed by the use of cloud services.
“What we are seeing from this report is that there are no consistent policies in place to manage the security, compliance, governance, and legal risks of cloud services,” said Rajiv Gupta, founder and CEO at Skyhigh Networks. “Our cloud usage analytics suggest that enterprises are taking action on the popular cloud services they know of and not on the cloud services that pose the greatest risk to their organization. Lack of visibility into the use and risk seem to be crux of the problem.”
Findings provide significant food for thought
At a high level, the report contains some good news about cloud service adoption:
- 2,204 cloud services are in use across three million users across financial services, healthcare, high tech, manufacturing, media and services industries.
- 545 cloud services are in use by an organization on average, and the highest number of cloud services used by an organization is 1,769.
In short, enterprises and their users see value in cloud services and rely on them heavily.
The graphic below shows the most popular sites, which include the obvious suspects although the order is interesting, and the percentage of service type. Not surprisingly content sharing service share top usage with social media with collaboration and file sharing not far behind.
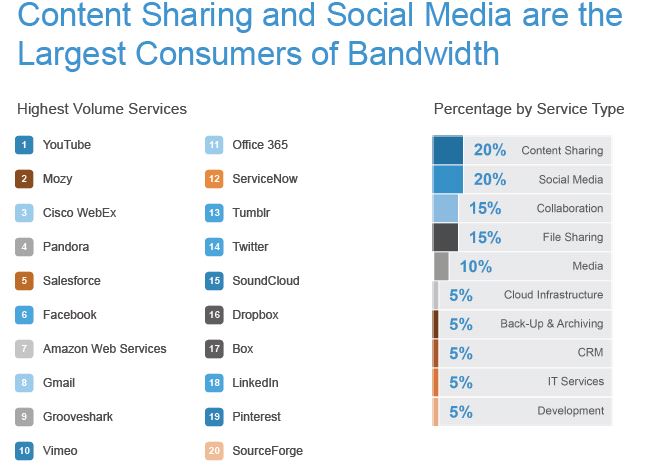
Source: SkyHigh Cloud Adoption & Risk Report 2013 (click to enlarge)
That said, addition findings become cause for concern and trends are certainly noteworthy. Results are presented with some provocative titles and the findings bear then out. They include:
It’s Not a Popularity Contest - It’s Risky Business
Corporate security measures are based on concerns related to productivity and bandwidth, or on the familiarity with the service as opposed to the risk of the services.
- Low-risk services are blocked 40 percent more than high-risk services.
- At 9 percent, tracking is the least blocked cloud service category despite the fact that it delivers zero business benefit and exposes organizations to watering hole attacks.
- Among the top 100 services used, the top 10 blocked services in use are Netflix, Foursquare, Apple iCloud, Gmail, Skype, Amazon Web Services, Batanga, Dropbox, KISSmetrics, and PhotoBucket.
Cloud-based Code Repositories Gain Momentum - Develop Responsibly
In the development cloud service category, cloud-based repositories have gained momentum.
- The shift to open source cloud-based code repositories presents security challenges as some sites are known to host malicious backdoors.
- GitHub is blocked 21 percent of the time but Codehaus, a high-risk service, is blocked only 1 percent of the time.
- The top 10 development services in use are MSDN, GitHub, SourceForge, Atlassian OnDemand, Apple Developer, Zend Server, HortonWorks Data Platform, CollabNet, Force.com, Apache Maven, and CodeHaus.
Microsoft - A Not-So-Sleeping Giant
While Microsoft may be falling out of favor with new users, it is too early to count it out.
- The third most widely used file sharing cloud service is SkyDrive
- The software giant dominates in collaboration with Office 365, Skype and Yammer in the top 10 of the most widely used services in this category.
- The top 10 collaboration services in use are Office 365, Cisco WebEx, Gmail, Google Apps, Skype, Yahoo! Mail, AOL, Slideshare, Evernote, and Yammer.
File Sharing Side Effects - Risk and Confusion
File sharing is widely used and the most misunderstood category by IT professionals.
- 19 file sharing cloud services are used by an organization on average, which impedes collaboration and increases security and compliance risks.
- 4 of the top most used file sharing services are high-risk.
- Box, the lowest risk file sharing service, is blocked 35 percent of the time, but Rapidgator, a high-risk service, is blocked only 1 percent of the time.
- The top 10 file sharing services in use are Dropbox, Google Drive, SkyDrive, Box, Hightail, CloudApp, Sharefile, Rapidgator, Zippyshare, and Uploaded.
IT lack of awareness
It is useful to return to the characterization of the cloud being untamed territory regarding risk. While the full report has a series of more granular charts involving poplar services and how often they are blocked or not blocked, the graphic below should be more than reason enough to download the full report.

Source: SkyHigh Cloud Adoption & Risk Report 2013 (click to enlarge)
Report methodology
As noted, the Cloud Adoption and Risk Report is based on data from more than three million users across more than 100 companies spanning financial services, healthcare, high technology, manufacturing, media and services industries. The top 10 services are based on the number of users of the service. The risk of each service is based on Skyhigh CloudRiskTM, which assigns a one-to-10 risk rating based on detailed, objective and weighted assessment of more than 30 attributes across data risk, user risk, device risk, service risk, business risk and legal risk. In fact, check out an insightful infographic SkyHigh has put together for the visualization of more useful fast facts on all of this.
We keep hearing about the explosion of vectors of vulnerability to stored data and data on the fly and how this has ratcheted up enterprise concerns about risk mitigation and increased interest in security solutions to address gaps in protection. What this report highlights is that as a result of the extraordinary use of cloud services, IT needs to be focusing even more attention—devising, implementing and enforcing policies and rules—that specifically target cloud service usage by employees.
The goal should not be obviously to prevent usage, especially since as other reports have shown people including C-levels will use what they value regardless of the rules, but rather to find a happy medium where popular services can be used for professional (and dare I say personal) benefit but done so safely and securely.
Edited by
Alisen Downey