There are two disquieting developments that security watchdogs at Cisco and Fortinet are discussing online. Because they are related and have to do with the increased risk exposure enterprises and users have to using old operating systems, particularly the looming end of life support of by Microsoft of Windows XP on April 8, hopefully this is a call to action for those who are vulnerable.
Please note that I am providing the links to the respective blogs on these items below. It is important that you read them in their entirety.
Cisco security pros find Linux 2.6 kernel have been compromised
The first item to note as the sub-headline states was the publication on March 20 of a blog by Martin Lee, Technical Lead, Threat Intelligence, Cisco Security Intelligence Operations entitled, “Mass Compromise of the Obsolete.”
As Lee outlines, Cisco has recently observed “a large malicious web redirect campaign affecting hundreds of websites. Attackers compromised legitimate websites, inserting JavaScript that redirects visitors to other compromised websites. All of the affected web servers that we have examined use the Linux 2.6 kernel….It is possible that attackers have identified a vulnerability on the platform and have been able to take advantage of the fact that these are older systems that may not be continuously patched by administrators.”
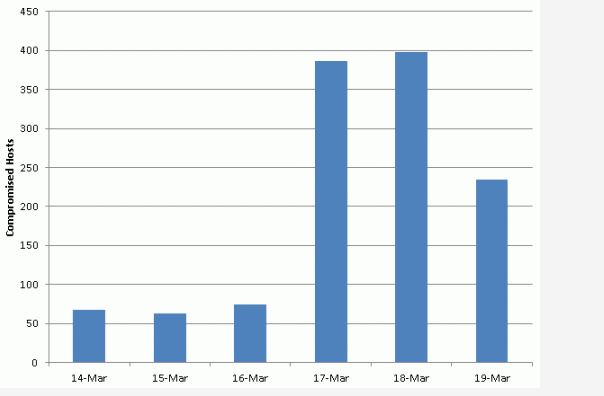
As the chart from Cisco illustrates, this bad boy is spreading fast.
He goes on to explain how this is done:
The attack itself happens in multiple stages. Attackers compromise an existing website, append a line of JavaScript to multiple .js files hosted on the site. This causes visitors to load and run a new JavaScript file served from a second compromised host. Utilizing a two stage process allows attackers to serve up a variety of malicious content to the visitor. We observed the second stage sites serving what appears to be pay per view fraud pages, where the visitor’s browser loads multiple advertisements to generate revenue for the attacker. However, there is anecdotal evidence that visitors have been infected with Trojan malware as part of this final step.
There are additional charts and advice in the blog, including the suggestion that organizations despite potential disruptions to business as usual need to weigh the risks of using operating systems that old and either unmaintained or unsupported. These systems need to be upgraded, monitored to detect to assure they have not been compromised and ideally should be replaced.
The Windows XP problem
Lee sites as an example of an old OS that needs to be watched Windows XP. It happens to be a perfect segue into the Fortinet blog by Guillaume Lovet, Senior Manager of Fortinet’s EMEA FortiGuard Labs, Will Windows XP be the new playground for cybercriminals after April 8, 2014? In short, the answer to this question is contained in Lovet’s conclusion:
“Understand that the key to staying on Windows XP is not being connected to the Internet. If that’s not possible, it’s highly recommended that you migrate to another operating system because it is certain that there will be an upsurge of attacks targeting XP vulnerabilities to extract sensitive information (competitive information, credit card numbers …) from these systems.”
While Lovet starts his blog by saying it is not clear that after April 8 you or your company will become a target, his caveat above that the only way to stay safe is to not have Windows XP connected to the Internet says all you really need to know.
Again, it is urged that you read the blog in its totality. Lovet walks readers through why the decision to upgrade is not an easy one. This discussion includes the observation that there are not insubstantial costs that upgrading to a next generation OS are likely to entail, particularly the need to replace existing hardware as current systems may not be capable of running newer OSs.
To drive home the point about the serious nature of what is about to transpire, Lovet notes that 95 percent of automatic teller machines globally rely on computers running Windows XP, and the same is true of most of the SCADA (Supervisory Control and Data Acquisition) used by electric utilities. And, while he is careful to note that while the ATMs and SCADA devices themselves would be difficult to compromise because they are not directly connected to the Internet, it does make the calculus as to what to migrate, how and when that much more complex.
It turns out that April 15 may be a day of dread in the U.S. because it is tax day, but for those who are responsible for risk management April 8 is looming large in the window (pardon the play on words). This does not mean that day will be Armageddon, but it does mean that understanding its implications and having a plan that gets C-level buy-in is something that commands attention sooner rather than later.
Edited by
Cassandra Tucker