As you can probably imagine, being someone who is attempting to keep an eye and ear on the continuing Heartbleed bug (aka CVE-2014-0160), bug phenomena has become almost a full-time occupation. Let’s just say that my inbox is inundated almost hourly, and I feel an obligation to read each one. By the way, I can assure all of you who are sending me stuff I do read everything you send.
The good news is that remediation of almost all of the potentially exposed servers on public websites using the vulnerable OpenSSL for encryption has been implemented. Plus, there are lots of tools out there to help even the average user be more careful. This means, it is safe to surf and safe to change your passwords on all those public places you go.
That said, it should be noted that public sites are not the only vulnerable ones. As the Dmitri Alperovitch, Co-Founder & CTO of security company CrowdStrike wrote in an insightful blog, announcing the availability of the free to everyone CrowdStrike Heartbleed Scanner, there is a lot more that needs to be considered. This is especially true if you are an IT security professional.
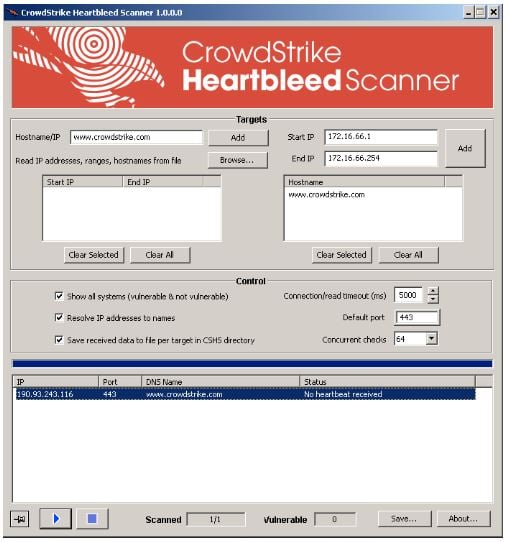
Source: CrowdStrike
Alperovitch explains, “We realized that there was a largely unmet demand for an easy to use UI tool capable of also scanning the internal networks and non-HTTPS services for this vulnerability since this problem is so much bigger than just external websites.” CrowdStrike’s Heartbleed Scanner addresses this important gap. Plus, the scanner outputs the contents of the 64kb of memory that a vulnerable server returns back to the heartbeat SSL request. This means you can see the extent of the impact of this vulnerability on your devices and services.
The new free tool enables scanning of Intranet SSL websites. It also allows for scanning of a host of other things including OpenSSL VPNs, Secure FTP servers, Databases, Secure SMTP/POP/IMAP email servers, routers, printers, phones, and anything else that may have been compiled with OpenSSL 1.0.1-1.0.1f.
As the company says, “Long story short, the Heartbleed vulnerability allows people to request chunks of memory from target servers. This memory often contains keys, passwords or other juicy bits of information that would otherwise be inaccessible. This affects certain versions of OpenSSL that allow anyone to specify how much information they want from the server – i.e. untrusted input in a leaky “heartbeat” function – thus the name. Note that there’s also a client component that may also need to be addressed.”
The reason I plucked this item out of my overflowing inbox should be apparent. It reminds of one of my favorite hit songs by the Eagles, “Heartache Tonight,” which if you don’t have time to listen here is the first stanza and the refrain:
Somebody's gonna hurt someone
before the night is through
Somebody's gonna come undone.
There's nothin' we can do.
Everybody wants to touch somebody
if it takes all night.
Everybody wants to take a little chance,
Make it come out right.
There's gonna be a heartache tonight,
a heartache tonight, I know.
There's gonna be a heartache tonight, I know.
Lord, I know.
Heartbleed, like so many of the malware that is out and about, can have greater impact than what was exposed in the first instance. What CrowdStrike rightfully is pointing out is don’t rest on your laurels and make sure everything that needs to be protected really cannot be compromised. The scanner is the right hammer for hitting all of the nails that need to be pounded to secure your enterprise. After all, even just one loose floor board can sink a ship if not properly secured. There does not have to be heartache tonight.
Edited by
Alisen Downey