It took less than a day for the imbroglio in the U.S. over the National Security Agency (NSA) compelling Verizon (via until June 5 a secret court order) to turn over phone records to explode. As predicted, this became the top news item of the day, which meant it was only a matter of time before there would be more information, either purposely leaked or uncovered by a now totally engaged investigative news community, about NSA best/worst practices.
The latest bombshell was the revelation in the venerable Washington Post that a top-secret program called PRISM, authorized by federal judges working under the Foreign Intelligence Surveillance Act (FISA), has allowed the U.S. intelligence community to gain access to the servers of nine internet companies for a look at what I like to call, “E”verything.
As the story turns
There are so many media folks covering the news and all the angles of this story that I will leave it up to you to check your favorite news sources as this unfolds. As this is written, there are a few things of note as we all try to sort through the babble.

Image courtesy of Shutterstock
First. The Washington Post story cited confidential slides it obtained of the PRISM program showing that NSA can directly mine data from Microsoft, Yahoo, Google, Facebook, PalTalk, AOL, Skype, YouTube and Apple. This led Twitter to brag about not being on the list.
Second. The companies listed above predictably denied, in almost identical language, that they have provided any government organization “direct access” to their servers. In Washington-speak, during the Watergate years this became known as the “non-denial denial.” In other words, they are not saying they are not sharing data with the NSA and it seems likely that this all stands on the definition of what really constitutes “direct access.” Hint, hint -- it is probably semantics.
Other predictable developments included pronouncements from various quarters, politicians as well as noted talking heads and intelligence “experts” about the value of both the phone record info and PRISM. It has been noted almost ad nauseam at this point that much of President Obama’s daily intelligence briefing is based on information gleaned via PRISM.
Finally, and again predictably, the intelligence community and its allies are outraged that their supposedly secret activities have been exposed and there are promises that those who have leaked this information will be pursued and held accountable for what the government sees as creating a real threat to national security.
In a move to assuage some of the anger over both surveillance programs yet make a point to those who like to expose such things, Director of National Intelligence James Clapper says he will be declassifying details about the phone call program, which he characterizes as legal, limited and necessary to detect terrorist threats. Clapper says every three months, a court reviews the phone records issue and that records are only culled when facts show a terrorism connection. This tracks with the defense that has been put up that since the program is using the data to spot trends based on excessive calls to non-US citizens who are targets of interest the public need not be concerned that their calls are being listened to unless they are doing something that rises to the level of being suspicious.
Like me, some members of Congress are vowing to change the phone records program, which interestingly enough, they voted to authorize out of fears concerning the lack of boundaries as to what constitutes virtual voyeurism versus legitimate intelligence work.
Clapper also admonished those who think they are doing us a public service by bringing such programs into the sunlight to, in essence, stop aiding the enemy. This is a classic stance that seems at odds with the world today. I am obviously no expert on national security matters, but it is hard to imagine -- especially since what we know about all the steps the late Osama Bin Laden took to evade electronic detection -- that those who wish to do the U.S. and its citizens harm believe our intelligence community is not using every means available to track them. In fact, it can be argued that the current revelations could be useful in sending a message to our foes about the lengths our intelligence community is willing to go.
All of this is going to be thoroughly vetted in the next few days. It certainly is going to make this weekend’s talk shows “must see TV.”
Back to the “breach of trust” issue
In my previous commentary on the call records revelation, I noted that, at least for me, what was at stake regarding intelligence community surveillance of seemingly all of us comes down to a matter of trust. I think it has been breached -- or if not so, at least severely and possibly catastrophically broken -- given the age of distrust we already live in.
There used to be a joke many years ago that said, “What are the three biggest lies you have heard lately?” The answers back then that still seem applicable were:
- The check is in the mail
- The Porsche is in the driveway
- We are from the government we are here to help
The last one goes to the heart of the concerns of now both current surveillance issues. It raises two important issues that cry out for resolution:
1. In a digital age, what are the boundaries for determining what is legitimate surveillance versus creepy and creeping Big Brotherism?
2. Who is watching the watchers?
In regards to the first question, I understand the intelligence communities’ zest for more information and secrecy. However, on the phone records one, the fact that there was a mandate to keep this secret unfortunately created the impression that there was something being hidden regarding the level of threat we face that meant the scope of surveillance needed expansion. In fact, the revelation of PRISM amplifies this. We still do not know why the Verizon request was made and what was so extraordinary that the FISA court said yes. Can we really now trust the NSA when it says it is not listening to content? Let’s just say they now have a credibility perception issue that all of the back-peddling on “legal justifications” will be hard to dispel.
That leads to the possibly more interesting second question. The old sage Alfred E. Newman probably sums it up best when he says:
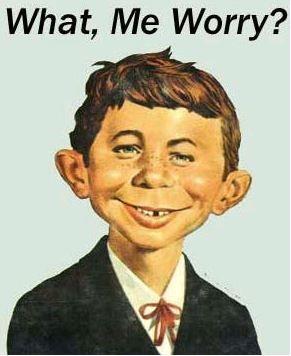
The answer is YES!
The intelligence community will do what it does best, i.e., remain suspicious of everything and and push for maximum information. The executive branch looks to that community for its advice based on its expertise and the facts are that we need them to stay in character.
However, if the FISA court is going to rubber stamp requests, its value and judgment should be cause for concern. The U.S. has a system of checks and balances for a reason. It is the role of Congress to provide oversight. Assuming the respective intelligence committees in the House and Senate knew about the phone initiative and PRISM, based on what they are and are not saying indicates a failure to question all of this. That is very troubling. It seems time for the intelligence committees to obtain more intelligence and act more intelligently and responsibly.
Who is watching the watchers is supposed to be the check against excessive use of authority. I am all for letting those with evil in their hearts be tracked, monitored and “taken off the playing field” when called for. The problem is that is in a free society we can’t all be viewed as suspects and, until there is a good explanation for all of this, the perception that government cannot be trusted is only going to be exacerbated.
At the end of the day, this comes back to the simple question of “whom can you trust?” It would be nice to have an answer to that one that is believable. Let’s hope we get one in the next few days and that it can stop the leakage caused by the perception of a breach before it becomes an unstoppable flood.
Edited by
Rich Steeves