With all of the outages, breakdowns, systems failures, hacks and other reasons why the likes of NASDAQ, Amazon, Twitter, Google, Tumblr and Microsoft have gone offline the past few days, you may have missed some other “incidents” that are equally if not more disturbing. In fact, with a big tip of the hat to Cisco, and Jaeson Schultz of the company’s security team in particular, here is a link to what is absolutely a must read blog from Aug. 22.
I will recap briefly why this is mandatory reading. IT starts with the blog’s first paragraph regarding ShareThis.com being hacked by the Syrian Electronic Army on Aug. 21. The reason to pay attention is that through its widget, “ShareThis interacts with more than 94 percent of U.S. Internet users across more than two million publisher sites and 120+ social media channels.” And, on the evening of Aug. 21, 2013, ShareThis reported “technical difficulties.”
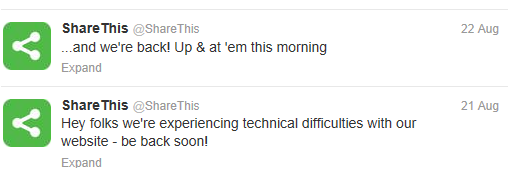
Source: @ShareThis
Schultz notes that GoDaddy holds the domain name registration for ShareThis and that its nameservers are supposed to point to Akamai, but on Aug. 21, they were pointing to Syrian Electronic Army nameservers.
He further explains that the bad guys are unfortunately spreading their malice. The Syrian Electronic Army hit Outbrain last week, which means they are not just doing frontal assaults on large media companies but are now targeting third-parties, thereby exploiting additional vectors of vulnerability to the proper functioning of commercial sites, not to mention creating user mayhem.
While Schultz provides a precaution we should use when visiting media sites, the example used – a plugin for Firefox – is not the browser of preference for most people.
More importantly is a question raised by TMC CEO Rich Tehrani about whether state-sponsored terrorism was behind the attacks on commercial sites.
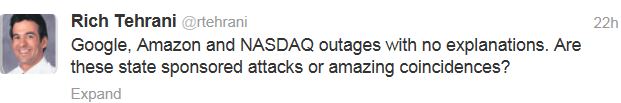
Picking up on Rich’s question was USA Today, which leans toward the explanation that the outbreak of problems is not an amazing coincidence.
Following all of the cyber attacks, threats and latest twist on how to behave poorly has become a full time and contact sport. What all of this should serve as for those C-levels who have been listening to their IT departments about the need to target and upgrade their risk mitigation investments is that it is not just time to listen but to act.
Schultz correctly points out the diabolical nature of the cyber terrorists going after “the weakest link.” Obviously the solution is to make all of the links stronger even though it is complicated and will take time. However, since we have transcended the time when hacking was a sport and not a business or a weapon of mass destruction funded or certainly encouraged by various governments, this is a problem that cannot be put on the back shelf for later discussion.
If you have not bookmarked various security update sites and blogs for alerts, or even if you have, Cisco’s is one to add to your favorites.
Edited by
Alisen Downey