For those who may not be aware, every year around this time management and consulting firm PwC publishes a comprehensive report of the state of global information security. It covers a number of critical vertical markets, and is always one of my ‘must reads,’ in general. I had an opportunity to review the telecommunications industry findings section of the 2014 Global State of Information Security Survey ®. It comes with the rather intriguing title and subtext:
“Defending yesterday. While organizations have made significant security improvements, they have not kept pace with today’s determined adversaries. As a result, many rely on yesterday’s security practices to combat today’s threats.”
It is why the findings are, in a word, “illuminating.”
The top-level findings provide a flavor of why this is something I like to spend some time reviewing. Based on responses from 456 senior telecom executives, the report found that:
- 53 percent of the respondents saw themselves as industry front runners in terms of securing their operations and protecting their and customer information; however,
- 28 percent say they are better at getting the security strategy right than actually executing the plan.
In other words, like most things the devil really is in the details, and to use another well-worn phrase “actions speak louder than words!”
Telecoms are under attack and spending more on protection with positive results
As noted above, this is a comprehensive and thought-provoking report that is full of useful charts and graphics. To whet your appetite I thought it would be useful to produce a few. The reason is that despite what you might think there is some good news in this sector. In fact, as the first graphic demonstrates the detected number of security incidents fell 17 percent from 2012 -2013, and the even better news not shown here is that the financial losses associated with such incidents decreased 34 percent in that time period.
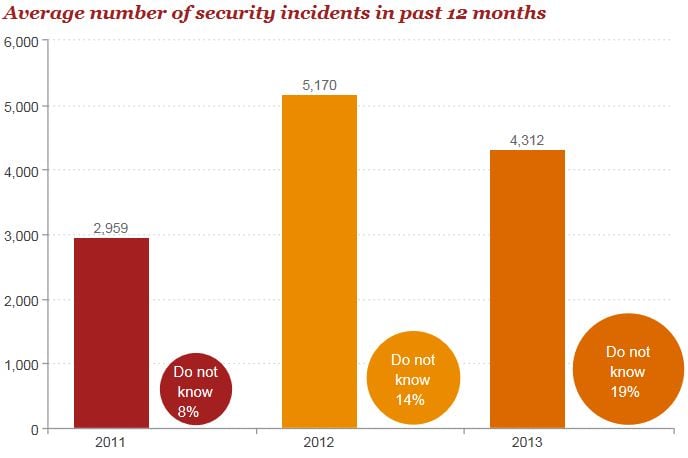
Source: PwC 2014 Global State of Information Security Survey ®
It is also of interest that again despite the headlines, it is not the barbarians at the gate that are the biggest security threats for telecom providers but current and former employees and trusted advisers who are identified as the estimated top sources of incidents.
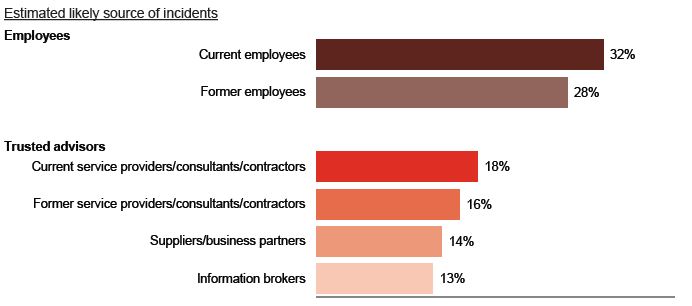
Source: PwC 2014 Global State of Information Security Survey ®
Among other key findings were:
Mobility has generated a deluge of business data, but deployment of mobile security has not kept pace – smart phones, tablets and the BYOD trend have elevated security risks, yet only 45 percent of telecom respondents have launched mobile security strategy initiatives this year (just a one percent increase from 2012).
Security budgets increased while confidence in programs decreased – Although telecom information security budgets increased to an average of $5.4 million (a 35 percent gain over last year), confidence in security activities decreased from 87 percent in 2009 to 71 percent this year.
When you peel the onion back on the confidence item it is telling. CEOs have a much rosier view than CFOs.

Source: PwC 2014 Global State of Information Security Survey ®
The report also answers some questions that are things security vendors are going to need to review.
For instance, in answer to the question, “What are telecom companies prioritizing?” it turns out that as PwC says, “Knowledge is power.” Respondents are prioritizing technologies that can help gain a better understanding of threats, as well as improve security for mobile devices. In fact, 32 percent say mobile device security strategy is a top priority for the next 12 months.
And, to the critical question of where things can be improved when it comes to security, two areas of concern with top of mind:
- Collaboration: Foregoing a powerful offensive tool, 23 percent of telecom respondents do not collaborate with others to improve security with 32 percent stating the main reason is concern that a competitor would use such market information against them.
- Security for the Cloud: While half of telecom respondents report using cloud services and 57 percent say the technology has improved security, only 20 percent include provisions for cloud security in their company’s security policy.
I will not spoil the rest of what is as noted at the top an illuminating report. The confidence discrepancy stands out as probably because the CFO has overall risk mitigation responsibilities and they are always fearful that not enough is being done.
That said, you will see that PwC’s title has substantial validation. Security investments while they have paid short-term dividends have mostly gone to tried and true tools like firewalls, web content filters, anti-virus and malware protection, etc. However, the fear is those “block and tackle” programs are not pointed at where the vectors of vulnerability are increasing.
In fact, the findings at the back of the report about the lack of deployment of technologies that can provide better insights into today’s rapidly evolving risks is worrisome. The feeling of respondents that they are doing a poor and deteriorating job of adequately safeguarding high-value intellectual property (IP)—doing regular reviews of users and access, inventorying assets, having dedicated procedures for IP protection, and classifying the business value of IP—borders on astounding. Indeed, given the cost of IP litigation you would think this area would be highly secure with strict controls in place.
As I stated, the PwC annual survey is on my must read list. If nothing else, if you are in the telecom industry or are a security vendor who sells solutions into it, this latest version is one to download.
Edited by
Ryan Sartor