For many of us of a certain age the wildly original American improvisational rock band Phish is the gift that has kept on giving since the band was formed in 1983. For those uninitiated, or merely curious, here is a link to their YouTube channel where the current featured track is “Wombat” as performed 10/31/13 at Boardwalk Hall in Atlantic City, NJ. Clicker alert: Phish is an acquired taste.
With that as a segue the purpose here is to serve as a public service warning. It is to alert you to Phishes that you should not acquire, or even taste. I am referring obviously to the online malicious act of “phishing.” By now it is all too familiar to all of us since we have likely been victimized. Somebody contacts you online masquerading (typically these days very well unfortunately) as a trustworthy entity and we willingly had over personal information like passwords and credit card numbers only to find out our identity has be stolen. This quickly can become the gift that keeps on taking.
The holiday season unfortunately is when those with malicious intent are at their phishiest. After all, successful phishing is a function or exploiting human emotions—fear, greed, anxiousness, curiosity, compassion, getting a good deal—and there is no time of year like the holidays for these emotions to be available for manipulation.
Believe it or not, phishing knows no bounds. In short, you can be hooked not just at home, but increasingly at work as the bad guys use exploits to gain access to sensitive corporate information and not just to compromise individual easy marks. In fact, security firm PhishMe, vice present Scott Greaux is out with a nice blog about holiday themed phishing attacks.
And, while Greaux’s message should resonate all year long regarding the need to educate your employees to be mindful of “E”verything, the presentation of the holiday baddies is reason enough for a brush up on best practices.
So here you go on exploits to be aware of.
Holiday e-card:

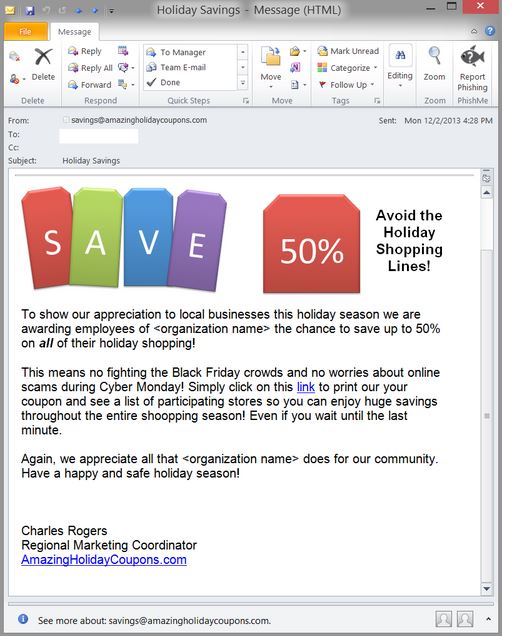
Short, sweet and very effective it turns out. Who does not like getting season’s greetings and discounts with participating merchants?
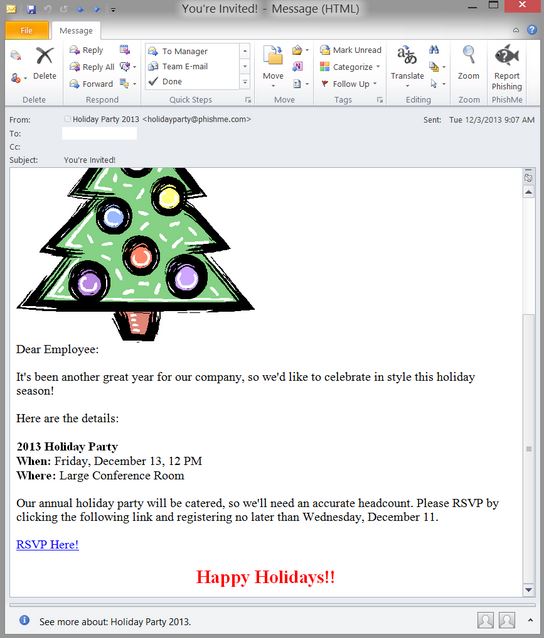
Equally as effective is getting enticed with a fake invite to your own holiday party as illustrated in the following example.

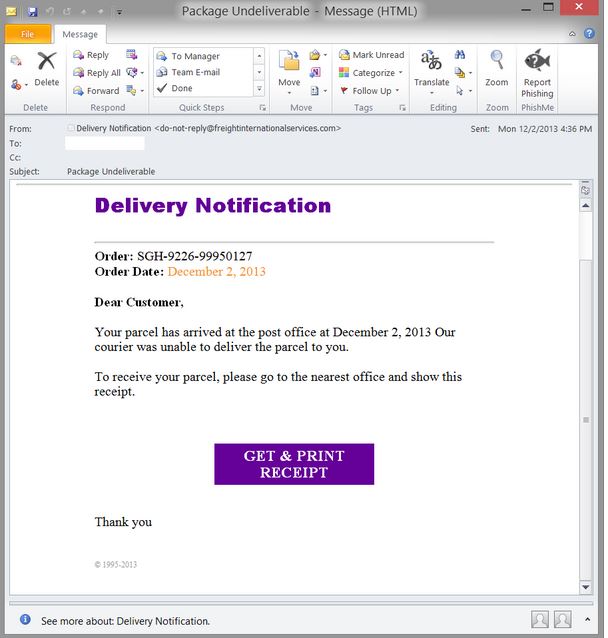
And, there is the always popular, you have a package waiting scam.

Greaux also warns that inside the enterprise a lots of avenues of mischief to be exploited in terms of getting you to click. This includes such things as emails about your end of year PTO balance, expense reports and other year-end information status requests/demands. Plus, whether at work or online at home, your inbox this time of year is filled with charities seeking money and all types of travel alerts.
This may be the season to be jolly and charitable but it is also clearly the season to be careful. I think I will leave my Phishing to the music variety on trusted links to YouTube or downloads from trusted sites, and leave the rest to a combination of my spam filer and delete button. The big thing to keep in mind is once you click open, you may have opened an attack, and that is something that can be a lot worse than the smell of rotting fish.
Edited by
Cassandra Tucker