For those of us of a certain age, the American humor publication Mad Magazine (it was only in print back then) was a must read. In fact, not only did its fictitious mascot Alfred E. Neuman grace the cover of numerous editions of the pub, but his poster (see below) with his most famous saying hung in many a rebellious teenager’s room.
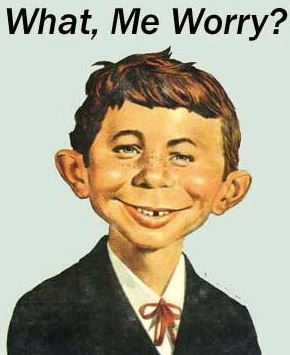
Source: Mad Magazine
The reason to cite Alfred is because of the daily drumbeat of data breaches that have seen the personal information of millions of Americans compromised on almost a daily basis. Indeed, while today’s headlines are about Apple’s cloud service being the source of salacious photos of celebrities, the list of major retailers and financial institutions what have been hacked has grown so large in recent months that a question to ask is, “Who has not been breached?” Unfortunately, with JPMorgan Chase and possibly other large banks, as well as Home Depot, added to the list just this past week, that list of those not yet hit gets smaller by the day.
While Alfred may not be worried, an unpublished research from WP Engine - an SaaS content management platform for websites and applications built on WordPress - has announced the results of its WP Engine Online Privacy Study. The survey, fielded by Harris to 2,100 U.S. adults and developed by WP Engine using the company’s expertise in content management and website hosting, examines consumer privacy concerns. It turns out that not only are American citizens worried, but 95 percent of those surveyed said they would take some kind of action if they felt their online privacy was being threatened.
In descending order, the list of actions consumers would take is as follows:
- Changing a password (79 percent)
- Deleting or unregistering from an app (57 percent)
- Reporting a company (56 percent)
- Changing email address (48 percent)
- Changing credit cards (48 percent)
- Deleting all social media accounts (42 percent)
- Change their name (7 percent)
- Move to a new home address (3 percent)
The last two are obviously drastic, but the numbers for the other actions speak volumes.
It does not look good going forward
The snapshot of attitudes today should be a reason for concern for online services, but the findings show that going forward attention really needs to be paid to consumer concerns. For example, almost 88 percent of respondents said that online privacy will be one of the biggest concerns for themselves over the next 10 years, for several reasons. These included because:
- We are becoming increasingly reliant on internet-enabled devices (59 percent)
- Social networking is exposing more of our personal information (57 percent)
- The government has too much access to information on its citizens (51 percent)
- We will be storing the majority of our personal data online/in the cloud (50 percent)
- Our locations can be easily tracked via GPS-enabled smartphones (50 percent)
- Our digital profile is more important than ever before for jobs, dating, and our private life (39 percent)
- More companies are using the facial recognition software to recognize citizens’ faces (24 percent)
Who and what worries us?
Delving a bit deeper, the survey also looked at which platforms concern Americans as likely sources of their personal information being compromised. To say the least, it should certainly be for thought for the entire online community. Concerns were as follows:
- Social media networks, i.e. Facebook (66 percent)
- Email (56 percent)
- Web browsers (52 percent)
- Search engines (45 percent)
- Social photo sharing platforms, i.e. Instagram (35 percent)
- Mobile apps (30 percent)
- Online dating apps (27 percent)
- Instant Messaging apps, i.e. WhatsApp (23 percent)
- Micro-blogging sites, i.e. Twitter (23 percent)
- Disappearing photo sharing apps, i.e. Snapchat (22 percent)
- Smart wearable devices, i.e. Google Glass (18 percent)
- Online games (17 percent)
“In today’s world of constantly streaming information and amplified volume of voice across online channels, it’s only natural that privacy has become a critical concern among Americans, and no doubt, the world at large,” said Heather Brunner, CEO of WP Engine. “It’s encouraging to see that as the online threat landscape changes over time, users are evolving with it, taking steps to protect themselves from harm.”
It should also be noted here that in a study done several weeks ago for WP Engine on consumer attitudes toward privacy that survey found Americans are concerned about their online privacy when:
- Accessing their bank account or financial data (71 percent)
- Shopping online (57 percent)
- Referencing photos of themselves online (27 percent)
- Browsing pornography (16 percent)
- Browsing social media while at work (14 percent)
- Checking out an ex on social media (10 percent)
- Looking up new jobs at work (9 percent)
Importantly, when it comes to ownership of content, the survey revealed that almost all Americans (93 percent) agree they should have full rights to some, if not all, of their information, albeit some info was of more concern than other.
As the headlines highlight, concern about personal data being compromised is certainly justified. Whether one believes or not that we have reached a tipping point regarding trust, which is the foundation upon which the Internet rests, that foundation has developed some big cracks that must be addressed before it crumbles.
The lists above show some obvious points of concern, but the fact that Internet of Things (IoT) capabilities are starting to make their appearance should serve as an industry wake-up call. Those working on IoT solutions are saying all the right things about security, but one can only postulate what precipitating event could turn promise into chaos.
At least when it comes to social media, messaging and the like, we have to provide some form of permission to have our data used. IoT, especially the surveillance aspects of it, but also what happens with all of that info from wearables that will be going into the cloud and turned into “actionable insights,” are activities that will not involve our permission.
As Brunner observes, the good news is that as the Internet evolves, consumer awareness and willingness to take actions to protect themselves is robust. That said, leaving protection up to the consumer in the long run seems like a counter-productive strategy. The old saying, “You don’t get a second chance to make a first impression,” is something to consider here. Translated it means that it is likely products and services that make securing of personal information a priority have a chance to use security as a valuable tool for creating sustainable value and competitive advantage.
Edited by
Alisen Downey