
When your website holds and transmits sensitive data or processes financial transactions, the last thing you want is for your cybersecurity to be compromised.
Once hackers successfully permeate your website, they can be in for a smooth ride toward stealing all your money, data, and other assets.
Data breaches persist until now, leaving companies with thousands to millions of dollars worth of losses and more.
This scenario raises the importance of cybersecurity even more.
Perhaps you’re asking, “how do hackers even get to invade my website in the first place?”
One of the ways is a scheme called brute force hacking.
Brute force hacking is the trial-and-error attempt to cracking your access details like usernames, passwords, and personal identification numbers (PINs).
As such, it’s more than essential that you shield your site from brute force hacking.
If you haven’t yet taken the right measures to do so, allow me to share with you six of them.
Let’s get started.
Use stronger usernames and passwords.
Brute force hacking works by repeatedly trying out different username and password combinations until cybercriminals have successfully accessed your account.
If that’s the case, then you can’t have weak and common website usernames and passwords.
Here are some tips to strengthen them:
Lengthen your password.
Some platforms have a minimum password requirement of six or eight characters. But, to increase your security, lengthen it by using 14 to 16 characters.
The longer your password is, the longer it can take for the hackers and their password-guessing software and techniques to break it.
Make them personal, unique, complex.
Lengthy usernames and passwords are good, but making them unique and complex is even better. Also, use something personally significant.
Combine special characters, numbers, and lowercase and uppercase letters.
For instance, instead of “myfbpassword12345,” use “My^44%fB33#$PassWoRd&179*”.
Avoid the following, as well:
- Replacing letters with numbers and putting numbers in order
- Using “qwerty” or “asdf”
- Using words from the dictionary.
The reason for avoiding these techniques is that hackers and software have already included them in their database of password-guessing attempts, making it easier for them to guess.
Manage your usernames and passwords.
When we have multiple accounts for our website, plug-ins, and tools — and therefore possibly different usernames and passwords — remembering them may be harder than we thought.
Managing your usernames and passwords is vital to defend your site against cybersecurity threats looming now.
To store your usernames and passwords safely, you can use third-party password managers like LastPass.
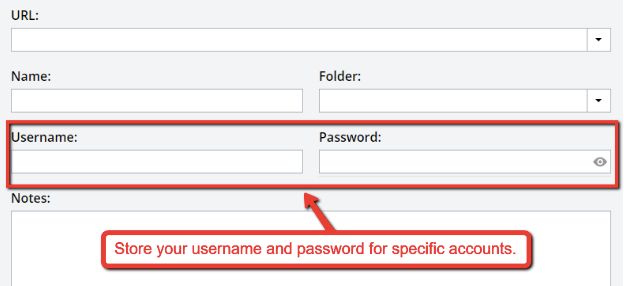
To add to your code storage, fill in the website URL, and your username and password for it.
LastPass acts as a vault and centralizes your access details securely.
You can even install this tool as a plug-in so that it automatically fills in those details when you log in.
Turn on a two-factor authentication system.
Another way to protect your site from brute force attacks is a two-factor authentication (2FA) system.
To sign in to your account, you normally have to enter your username and password.
A 2FA system, however, will go beyond that and you to authenticate your identity. It asks you to type in a unique code sent to you using some other means or device.
Many websites and email platforms formed already have the 2FA system option for you to enable.
To show you how it works, here’s an example from Facebook:
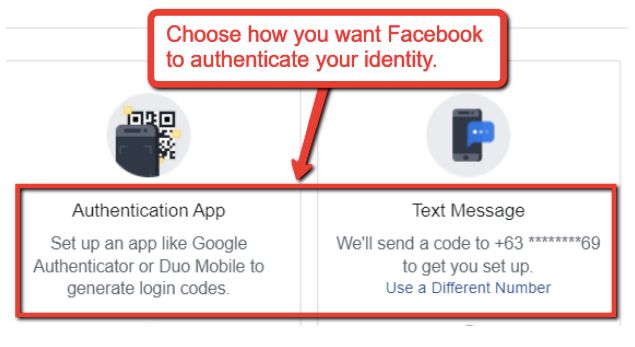
When you enable 2FA, Facebook asks you how you want it to authenticate your identity.
It can be typing a code sent via SMS or setting up apps like Duo Mobile to create login codes.
This technique helps hamper brute force hacking. Even if the cybercriminal succeeds in cracking your username and password, he still needs to type in codes sent to your devices.
Enforce pen testing.
Setting up cyberdefenses is good, but this does not yet guarantee that they can already resist brute force hacks.
You want to be confident and sure that your defenses are “tested and proven” robust and effective against such threats.
You can do that when you go through the cyber kill chain and enforce a penetration test (also known as a pen test).
In a cyber kill chain, you get to identify the stages and means that hackers can use to steal your data.
In the first stage, a hacker attempts to invade your account through brute force hacking, phishing, or others.
A pen test will then help you see if your site can protect itself against such attacks.
A pen test works by replicating a hacker's attack. In this way, you see the gaps your cyberdefense networks may have, and find ways to repair them.
To enforce a pen test for your site, you can tap reliable third-party service providers.
They have the necessary equipment and expertise to carry a pen test safely and without disrupting your company’s operations.
They can also explain the test results and elaborate on countermeasures and improvements you can take on.
Regulate the number of log-in attempts.
When you reduce the log-in attempts a user can make, you also lessen the chances of successful brute force hacking.
When the user reaches the set maximum number of failed log-ins, your site restricts the IP address for a determined period. It also temporarily denies further log-in attempts.
You can also use progressive delays. They are a better defense strategy, though more complex.
Progressive delays lock your account for a specific period after some unsuccessful log-in attempts. It then increases the lock-out time with every subsequent log-in failure.
When this happens, you prevent automated mechanisms from performing brute force hacks, and cyber attackers will find it pointless to continue.
Establish reCAPTCHA.
reCAPTCHA stands for Completely Automated Public Turing test to tell Computers and Humans Apart.
It is Google's way of protecting your site from spam and abusive activities commonly carried out by bots.
When Google finds an activity suspicious, it will ask you through reCATCHA if you are a bot or human. Here's how it looks like:
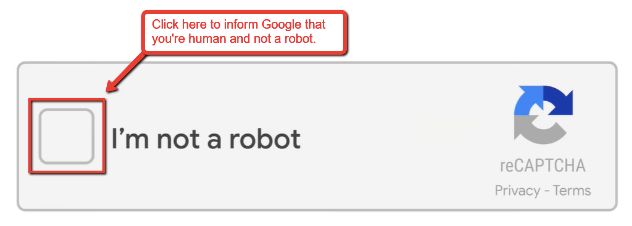
After ticking the box, Google will let you prove it by solving puzzles that bots can’t read.
The great thing about reCAPTCHAs is their user-friendliness.
Google ensures it’s not disruptive, and you can avoid crucial UX and web design mistakes that hamper your visitors from coming back.
You can set up reCAPTCHA for your site, too. Register at Google, get the keys and embed a specific type of code onto your website’s frontend.
That way, in case a bot visits your site, the reCAPTCHA can prevent it from entering and possibly brute force hacking.
Set up account lockouts.
You can also set up account lockouts to shield your site from brute force hacking.
Account lockouts take place when log-in attempts reach the fixed maximum number. The user’s account remains inaccessible until the site administrator unlocks it.
This situation can become risky, though, because hackers can cause several legitimate accounts to be locked out.
When that happens, more people will be affected ,and the administrator will have to deal with a heavy responsibility to resolve this.
Shield your site from brute force hacking.
Brute force hacking is no light matter because it attacks your first layer of defense.
If you don’t strengthen your cyber defenses, it may be too late before you realize your website management and assets are compromised.
That said, you should take preventive measures now, not later, to shield your site from brute force hacking.
If you found this post helpful, please share it with your colleagues. Cheers!